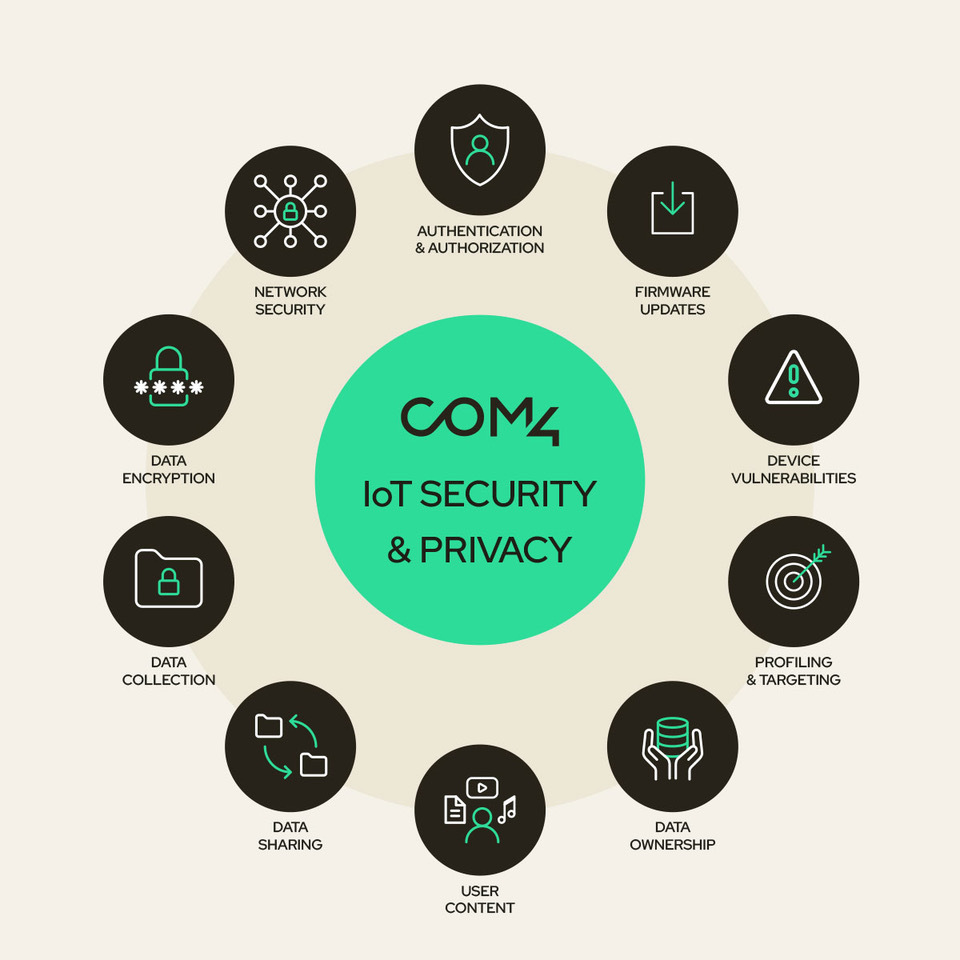
Below follows a set of key security advice we find to be important and that organizations should consider to protect their IoT investments and secure their IoT solutions. This will provide a solid foundation for a secure IoT solution, however be mindful that such a list will be non-exhaustive as most solutions have their unique characteristics and since the threats evolve over time. Therefore make sure to do your risk analysis and maintain a network security policy as part of your organization Information Security Management System (ISMS).
Secure your connected devices
One of the most common entry points for malicious actors is through vulnerable devices that are improperly secured, or not properly maintained. Whether your IoT devices is a custom developed embedded device, or a commercial off-the-shelf solution, various measures should be implemented to harden the device. To limit the attack vectors, only services needed for the specific application should be enabled. Only the network ports needed for the specific application should be open, and default credentials and usernames should be unique (per user and per device), strong passwords should be used, and these should be changed and kept on a principle of least privilege.
Physical access to the device should also be limited where possible, and any physical interfaces not in use on the device should be disabled. A tamper-resistant packaging can reduce any physical attack vectors in public available environments such as theft of SIM card for fraudulent use or manipulation of device.
Cellular devices can benefit from non-removable eSIMs soldered directly on the circuit board. The advent of iSIM also significantly reduces the SIM as a physical attack vector. These protections can also be supplemented by mechanisms from your IoT providers, such as locking the SIM card to the specific device and notify any change attempts, which is a feature that some Connectivity Management Platforms (CMP) support.
As the threat landscape continuously evolves it is important to have a good policy to keep firmware and software up to latest security recommendations, and having a method to identify and apply security patches in a timely manner. 
Secure your network solution
For the vast majority of IoT applications, full Internet access is usually not needed. Having full control over the network communication is essential. Both for securing the data from eavesdropping and manipulation, but also keep the network solution resilient to e.g. Denial of Service attacks.
A SIM card with Firewall filtered access can be used to only allow communication towards the endpoints in use. The most secure solution will be to use a Private APN with a VPN from the IoT Connectivity Provider that delivers the connectivity. If a total isolation from the Internet is possible from a solution standpoint, connectivity solutions with separate IP routing from the Connectivity Provider should then be explored. There are also several factors that should be considered for having a network solution that is resilient to outages, including redundant nodes and connections both at the core and in your particular connectivity. Choosing an IoT Connectivity provider with SIM cards with access to multiple radio networks will also mitigate any loss of connection based on local radio challenges.
A good collaboration with the IoT Connectivity Provider should also include capabilities within non-intrusive monitoring of traffic, behavioral analysis, and the ability to detect known and unknown anomalies, all of which contribute significantly to enhancing security. To handle incidents in practice, it is also important to use an IoT solution provider that offers good response times and communication during incidents so that you can manage the situation well for your own processes and customers.
Secure your data
Although device and application security address the endpoints of an IoT network, the core focus for stakeholders and potential threats remains the data being generated, transmitted, processed and stored. Encryption emerges as a powerful defense mechanism for protecting IoT data, both while in transit and at rest. For the transit, make sure to use IoT devices and backend systems that support suitable encryption for your solution and check that it is properly configured and maintained. A particular point here is that an IoT device is usually also provisioned with credentials, certificate files or API keys that must be kept secure and unavailable for unauthorized access. To avoid storing these data on e.g. flash memory, solutions like IoTSafe can be used to securely store application specific secure data on the SIM card with the help of inbuilt encryption and a tamper proof element. Regarding the encryption “at rest” it is important to use suitable encryption at the servers whether being in the Public or Private Cloud, as well as on any end point in your organizations, such as staff laptops and mobile phones.
Additionally, maintaining data sovereignty is a concern, necessitating robust security controls to ensure data remains encrypted across all states and is accessible only to authorized entities within designated domains.
Discover how Com4 can elevate the security of your IoT projects. For more information, visit our webpages on IoT security or talk to an IoT expert.